- User Rating Me
-
- Latest Version
- Phoenix 360
- License
- Paid
- Release
- May 30, 2019
- Ad Support
- No
- System Requirements
- Windows 7 / Windows 7 64 / Windows 8 / Windows 8 64 / Windows 10 / Windows 10 64
Download Phoenix 360 to Protect and Enhance your Digital Life
There are tons of harmful performance and security vulnerabilities that can affect your device in the worst way possible and steal your data in seconds. You should consider Phoenix 360 for a free download. Phoenix 360 is comprehensive privacy, security, and optimization package. This integrated security tool can help your system in a ton of ways. Read along this review to know more.
What’s new?
A few bug fixes and other enhancements.
Editor’s review
Phoenix 360 is an incredible application that protects your PC from crapware invasion, data theft, and more. The software ensures to not breach your privacy.
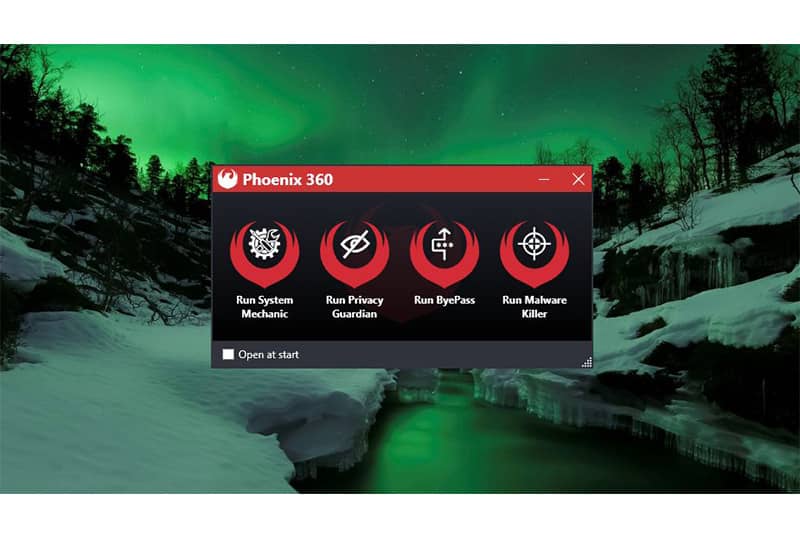
There are four segments in this package: System Mechanic, Privacy Guardian, ByePass, and Malware. With the help of these tools, users can fearlessly use their devices with the utmost freedom that there is.
Moreover, even the world’s most popular and trusted companies fail to provide the best protection to their personal data. Phoenix 360 has come with a concoction of all of its best products to provide its users the protection that they need on a regular basis.
Note: Phoenix 360 is now integrated into System Mechanic Ultimate Defence.
Features and Highlights
The following are the benefits and features offered by Phoenix 360:
Optimize Computer Speed
One of the most common issues that are used by PC users is the slow working of their system. The reasons for slowing down your computer can be numerous. To fight them all, you need to have a single comprehensive solution. Phoenix 360 has enough capabilities to boost up your PC and optimize it in the best possible way.
Secured Privacy
Privacy Guardian is a part of the whole Phoenix 360 series. This tool protects your online privacy from threats to browser fingerprinting scripts. It does so by scrambling the data they are relying on to fetch all of its personal data. It protects all of your personal information that might leak your sensitive data.
Safeguard Credit Cards and Passwords
bypass is another included tool in Phoenix 360. It is designed to provide you with the best potential of your digital life while securing it. bypass is a platform-agnostic and password manager that protects your online purchases information. It ensures to protect your credit card information.
Blocks Malware
System Shield is an incredible anti-malware solution that manages to deploy reactive and proactive malware detection strategies. A reactive strategy identifies viruses using the published malware and virus signature detection. As far as the proactive strategy is concerned, it uses a decent monitoring technique that categorizes files to see whether they are capable of harming your PC.
Recovers Lost Data
The search and Recover deploy tremendous technology that allows you to recover items. this software allows you to retrieve all of your accidentally deleted music, documents, emails, videos, and more with mere effort.
Pros of using Phoenix 360
The following are the perks of using this security tool:
- Easy-to-use
- Powerful security tools
- Highly-compatible
- Cookies eraser
Cons of using Phoenix 360
The shortcomings of using this software are below:
- Individual registrations
Frequently Asked Questions
For further reference, take a look at the most frequently asked questions by the users:
Q1. Is Phoenix 360 safe?
Yes, Phoenix is a great security tool that is trusted by numerous users. This all-in-one solution provides you with all the tools you need to protect your system from any given fallout.
Q2. Does Phoenix 360 have a free version?
No, Phoenix 360 is purely a paid security tool. However, this one is way ahead of its competitors in terms of pricing. It is priced at $74.99.
Q3. How do I download and install Phoenix 360?
To download and install the application, follow these steps:
- Click on the download button mentioned above.
- Once the installation file is downloaded, double click on it.
- Now, follow the on-screen instructions to buy the installation and license key to continue using the application.
Q4. What are the alternatives to Phoenix 360?
The following are the top alternatives to this program:
- LogMeIn Central
- Norton Antivirus
- End-User Endpoint Security
End-Note on Phoenix 360
To summarize this security tool it is safe to say that Phoenix 360 is surely a great program that can keep your device protected from every given angle. It has all the features you will ever need in security software. Download the latest version of Phoenix 360 on your Windows PC and see how it works for you.